Hacking in Cyberpunk 2077 allows you to take down your enemies, gather Intel, and earn extra cash without needing to draw your weapon. By just interfering with their Cyberware and tweaking a few things around, you will be able to get out of situations scotch-free
Hacking is divided mainly into two categories based on what it is being used for. The first is Scanner Quickhacks where you will be using hacking offensively, for combat purposes and recon. The second one is the Breach Protocol which allows you to hack Access Points and rewards you accordingly.
The path to master both is pretty interlinked so you can focus on one and the other will automatically follow. Like many other mechanics, Hacking too received a major refresher in the Cyberpunk 2077 2.0 update, so let’s see what has changed and how you can use it to your advantage.
How hacking works in Cyberpunk 2077 2.0
Hacking has received a few changes as well as some upgrades with the 2.0 update. To hack something you need a tool called Cyberdeck, which can be found in your Inventory by default. Each Cyberdeck has a limited RAM with some pre-installed and equipped Hacks, which are called Quickhacks.
Each Quickhack costs RAM and depending on its utility and strength, it differs in price. RAM is a rechargeable source that replenishes when you are not in combat, so you don’t have to worry about running out of it.
As you progress, you can pick up Perks and upgrades that will both lower the RAM cost of some Hacks and increase your RAM capacity. This allows you to quickly unleash powerful Hacks in quick succession with little to no downtime.

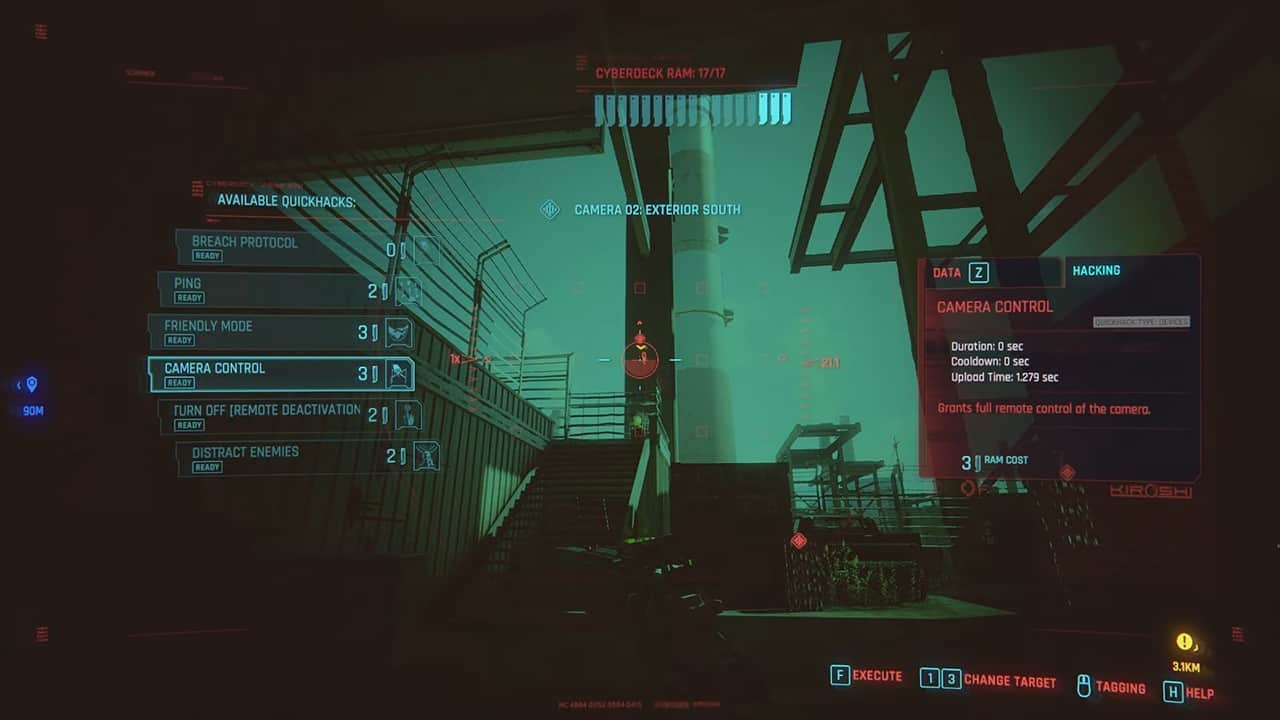
To hack something, you will need to scan the area and enemies to find hackable sources. These objects or Access points are highlighted on your scanner so you will know when there is a target. Simply hover over the object or enemy and a menu will open displaying which Quickhacks you can use along with their RAM costs and details.
Just choose the one you want to unleash from your list and you’re already on your way to becoming a Netrunner.
Quickhacks
Quickhacks are what allow you to move in and out of cyberspace as a Netrunner and bend it according to your will.
These Quickhacks allow you to spot and highlight enemies, cameras, explosives, traps, and turrets. You can also track the movement of targets, to see what their next move is going to be. Cameras can be taken over as well so you can move them out of your path or spy into enemy territory.
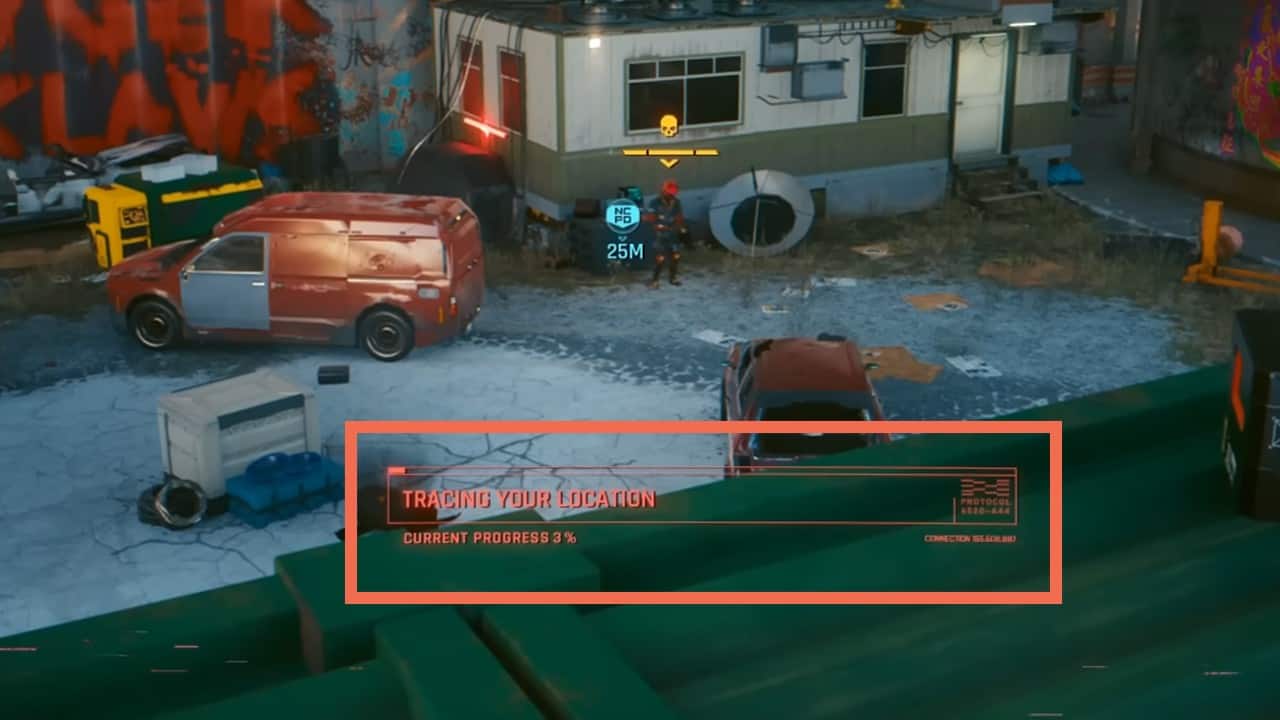
When you Quickhack something in Cyberpunk 2077, after the 2.0 Update, it now has a detection bar called the Trace Progress. It will be displayed on your screen once you start uploading a Hack onto the target.
This Trace Progress bar fills up gradually and increases the chances of you being detected by the enemy. Once the bar is full, they will be alerted, exposing your location. To stop the progress, you need to get out of sight, stop the hack, or take out the enemies in the area.
How Breach Protocol works in Cyberpunk 2077 2.0
Breach Protocol is a mini-game you encounter while hacking in Cyberpunk 2077. Before the 2.0 update, it shared its name with a Quickhack as well but it was removed and replaced with other skills.
During the game, you will be uploading Daemons by entering the right sequence onto your buffer before the timer runs out to get access to whatever you are hacking.
You will be coming across this mini-game when you hack into Access Points. These points are part of non-combative hacking where you will just be deciphering something or doing it for extra cash. Access Points are marked with a red Ethernet cable icon and are mostly present on computers, terminals, antennas, and cyber tech among many other things.
Breach Protocol Mini-Game

The mini-game has a grid filled with a random sequence of letters and numbers on one side with a sequence of three Daemons you need to enter on the other side.
During Breach Protocol in Cyberpunk 2077, you can only select an input from a highlighted row or column. To start things off, the first row is always highlighted with one of the correct sequences to choose from.
After selecting the correct cell, the corresponding column will be highlighted and its contents will be available for selection. You can select your second input now, and the corresponding row will become highlighted. This goes on till you have either successfully activated the Daemons or run out of inputs for your buffer.
Note that you can put in a few wrong ones along the way to make the right inputs available for you. However, there is only so much chance for failure so don’t overdo it if losing is not an option.
By entering all the available inputs, and uploading all three Daemons, you will be rewarded the Christmas Tree Attack Trophy in Cyberpunk 2077.
Best perks for hacking in Cyberpunk 2077
While both Intelligence and Technical Ability have some of the best perks for most builds, there are only a couple of perks that improve your hacking skills in Cyberpunk 2077.
For Breach Protocol, the only Perk left after the 2.0 Update is the Forcekill Cypher under Intelligence left Skill Tree. It reduces the sequences you need to hack into Access Points by 1.
For Quickhacks we recommend taking Overclock in the middle Intelligence Tree. It allows you to trade in your HP for RAM along with some additional buffs. Its secondary nodes also provide great RAM and damage-boosting sources, which you will naturally grab if you are a serious Netrunner.

Hacking tips and tricks in Cyberpunk 2077
The hacking and Breach Protocol mechanics can be a bit overwhelming at the start but do not fret. They are pretty easy to understand once you have spent a few hours in the game. Nonetheless, these tips will further help you tap into the mainframe of Night City.
Plan your route in Breach Protocol
The timer for the Breach Protocol mini-game starts after you select your first input. Before that, you have all the time to plan the route you are going to take for uploading maximum Daemons.
Upgrade your Cyberdeck
As you level up, your Hacks will start costing more RAM to match your current ability in the game. To make sure you don’t fall short on RAM after a basic hack, remember to level up your Cyberdeck as well.
Breach Protocol for farming cash
You can scan around the city and search for Access Points you can hack. Hacking into Access Points in Cyberpunk 2077 will get you some extra cash along with Quickhack Components that you can use for crafting Quickhacks. The more Daemons you upload, the better the payout.
Hack vehicles
Along with devices, you can also hack into Vehicles like cars to get a few more rewards. This will, however, require you to have a Cyberdeck equipped of either Tier 4 or Tier 5.
Restart your hacks
If you are about to fail, you can exit it completely to restart it completely. Since you can’t go back on the input, it’s great to restart your hacks if things don’t go your way.